Core problem: a single shared AI tenant feels efficient until cross-site data mixing, conflicting policies, or one incident forces a painful split
Main promise: clear isolation rules align blast radius, compliance boundaries, and operational ownership with how the factory network actually runs
Isolation is not paranoia. It is blast-radius engineering—the same instinct that drives network zoning, segregated admin paths, and careful separation between test and production. A single shared AI tenant can feel efficient until cross-site mixing, conflicting policies, or one serious review forces a painful split that should have been designed in from the start.
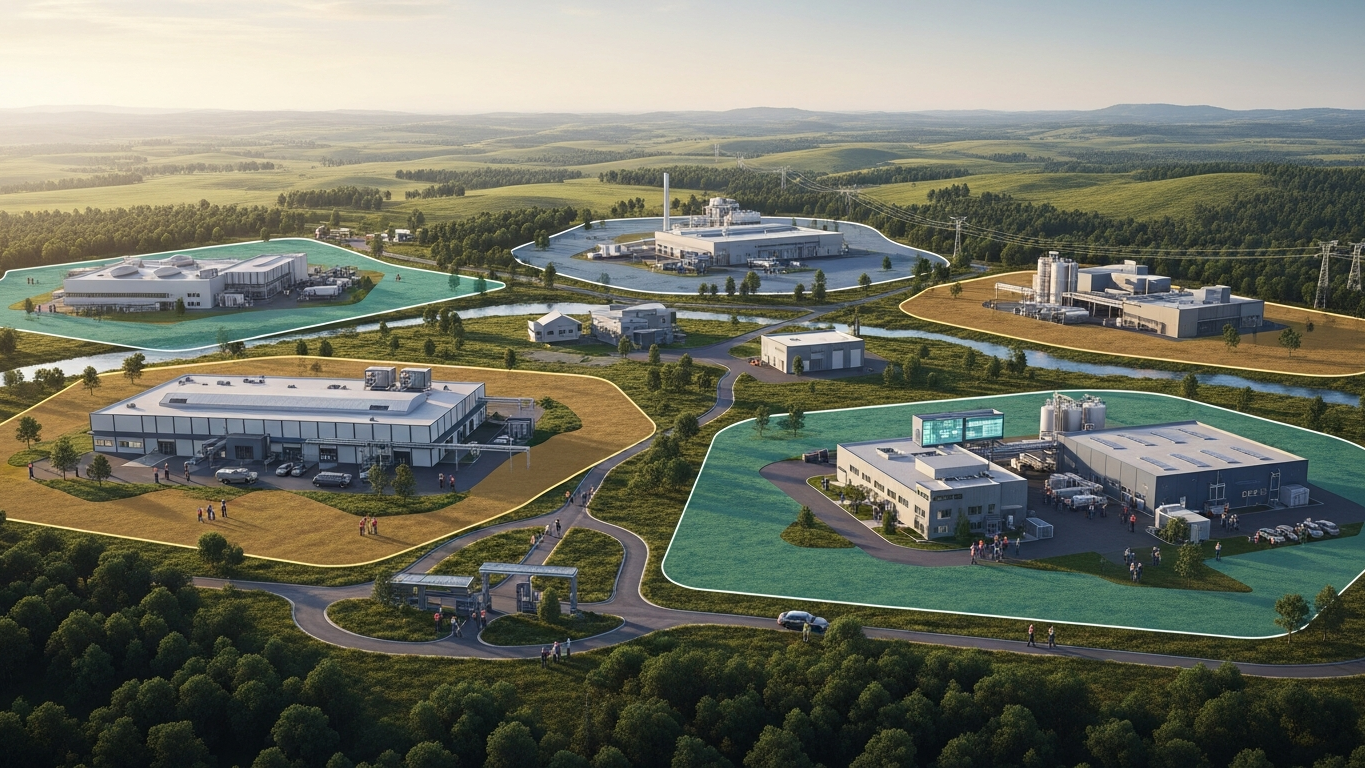
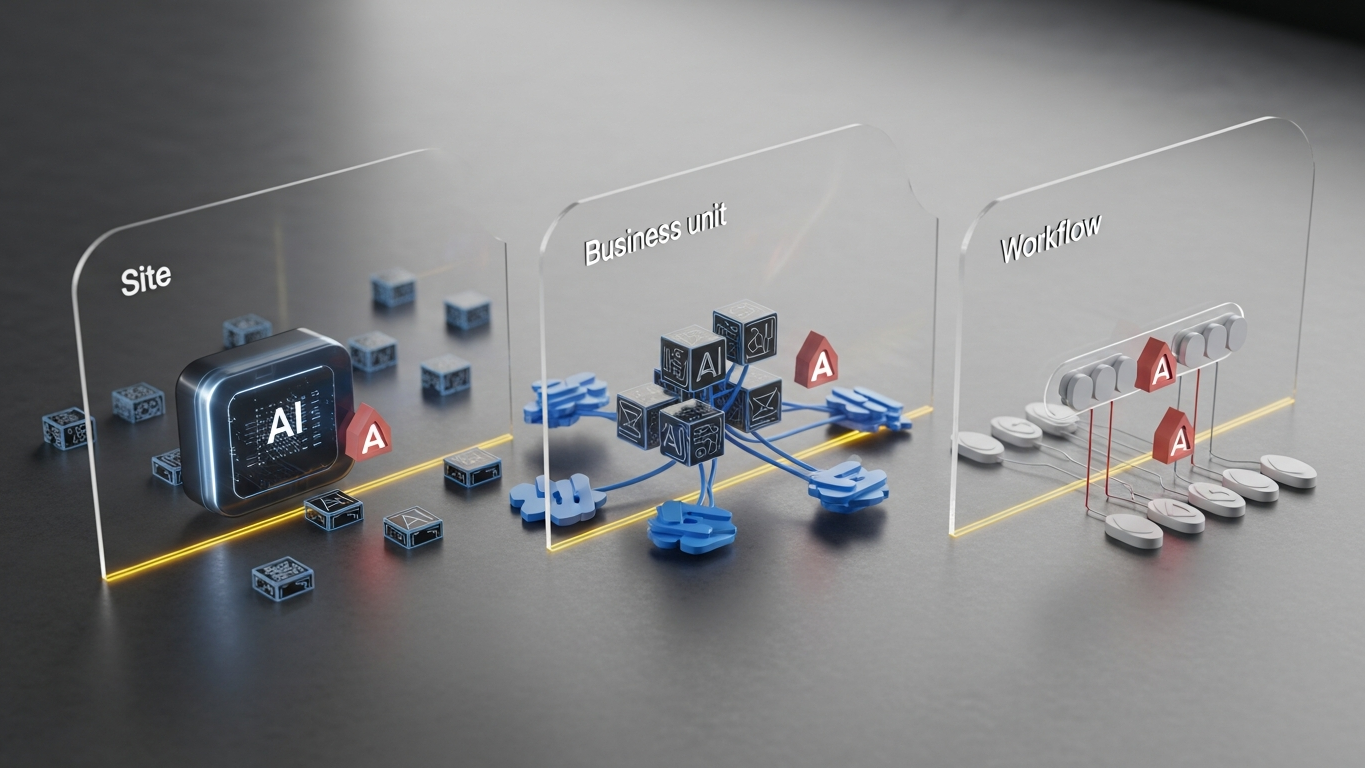
Isolate AI by site when plants operate under different regulatory regimes, data classifications, or labor and works-council constraints that make commingling costly to explain. Isolate by business unit when P and L, IP, or customer confidentiality must not commingle in logs and admin access. Isolate by workflow when a high-automation path touches actuation or safety-adjacent systems while other workflows stay analytical. The right unit of isolation matches the unit of trust—not the unit of procurement convenience.
Three isolation lenses
Regulatory and data class is the first lens because it is the least negotiable. If two sites cannot share the same backup jurisdiction or retention rule, they should not share the same AI runtime namespace—because an incident or audit question will not care that “it was cheaper on one contract.” Commercial and IP boundaries form the second lens. When business units protect distinct process IP or sensitive customer relationships, shared inference tenants create unnecessary forensic doubt after any leak suspicion: everyone becomes a suspect, and the investigation becomes political as well as technical. Operational and safety coupling is the third lens. Workflows that can influence physical state deserve harder boundaries than summarization of internal PDFs—not because summaries are harmless, but because the blast radius is different when recommendations sit next to execution.
What the stressful moment looks like
The case for isolation usually clarifies after a tense week: a quality escalation, a customer audit, or a security review that asks a blunt question—who else could have seen this payload, and under what account? If the honest answer is “we are not sure,” you have already lost the narrative battle. Isolation is how you keep that answer short and factual: bounded populations, bounded logs, bounded admin paths. It is not about distrusting your own sites. It is about making ownership lines crisp enough to defend when pressure arrives.
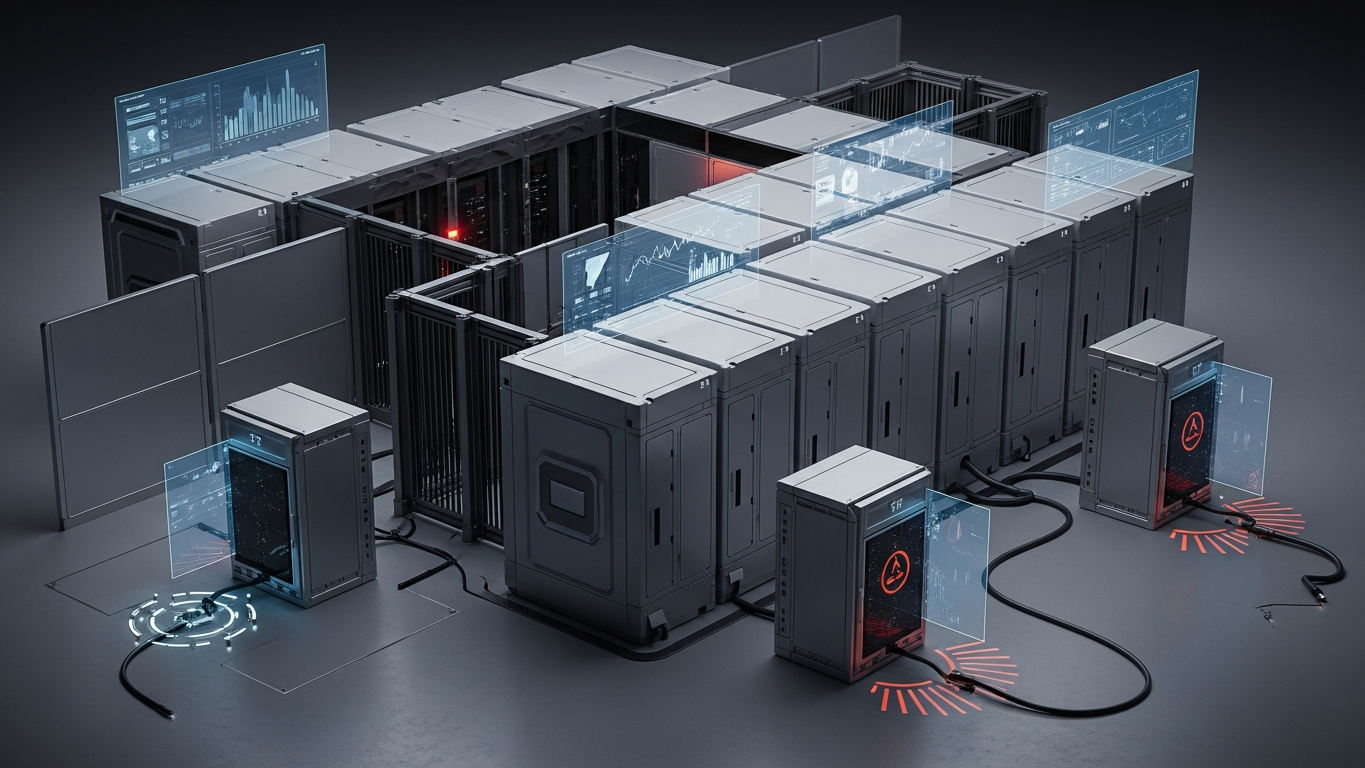
Shared tenancy can work when data classes are uniform, policies are centralized, logging is segregated with strong tenant separation, and no workflow writes to production systems without a dedicated approval plane—verify those conditions in writing, not as assumptions. If you cannot verify them, do not let procurement optimism substitute for architecture.
Site, business unit, and workflow isolation are trust-domain decisions; the platform has to offer deployment shapes that respect those domains without forcing one brittle global tenant. Vector supports that exercise: proprietary industrial AI with on-premise, private API, and isolated patterns, client data excluded from training the shared model, and industrial reasoning aimed at transformation work—so isolation choices land on architecture, not on consumer SaaS defaults.
Manufacturers should choose isolation granularity the same way they choose network zones: match the boundary to the trust domain, then scale inside the boundary with discipline.
Plant checkpoint
Treat “When a Manufacturer Should Isolate AI by Site, Business Unit, or Workflow” as a decision tool, not background reading. Before the next steering meeting, ask for one artifact that proves your posture—an architecture diagram, a training-policy excerpt, a log sample, a signed workflow classification, or a promotion record. If the room can only tell stories, you are still in pilot clothing. Manufacturing AI matures when evidence becomes routine: the same discipline you already expect before a line release, a supplier change, or a major IT cutover. That is the shift from excitement to infrastructure—and it is what keeps programs coherent across audits, turnover, and multi-site expansion.
If leadership wants one crisp decision habit, make it this: name what must be true before usage expands, then review whether it is true on a fixed cadence. That is how governance stops being a narrative comfort and becomes an operating metric your plants can execute.
DBR77 Vector supports stronger deployment boundaries so isolation choices map to on-premise, private API, and isolated operational patterns across sites. Review security or Explore products using Vector.