Core problem: many enterprise buyers know they need secure industrial AI but lack a concise checklist for evaluating deployment, governance, and data control before adoption
Main promise: manufacturers can reduce buying risk by using a practical enterprise checklist that covers the minimum conditions for serious AI deployment
Secure AI in manufacturing should not be evaluated through vague confidence. It should be evaluated through a clear checklist—the fastest way to reduce buying risk without lowering standards. AI buying often becomes too abstract: broad claims about security, privacy, governance, and intelligence stacked on slides. What enterprise teams need is a direct way to verify whether the system is actually ready for serious industrial use, not whether the demo felt impressive.

Why a checklist matters
Checklists force specificity. They turn “we are enterprise-ready” into answers your security lead can compare to how you onboard every other plant-adjacent system. They also protect the business from a common failure mode: a pilot that succeeds socially while failing structurally—because training defaults, logging, and deployment truth were never pinned down.
The enterprise checklist
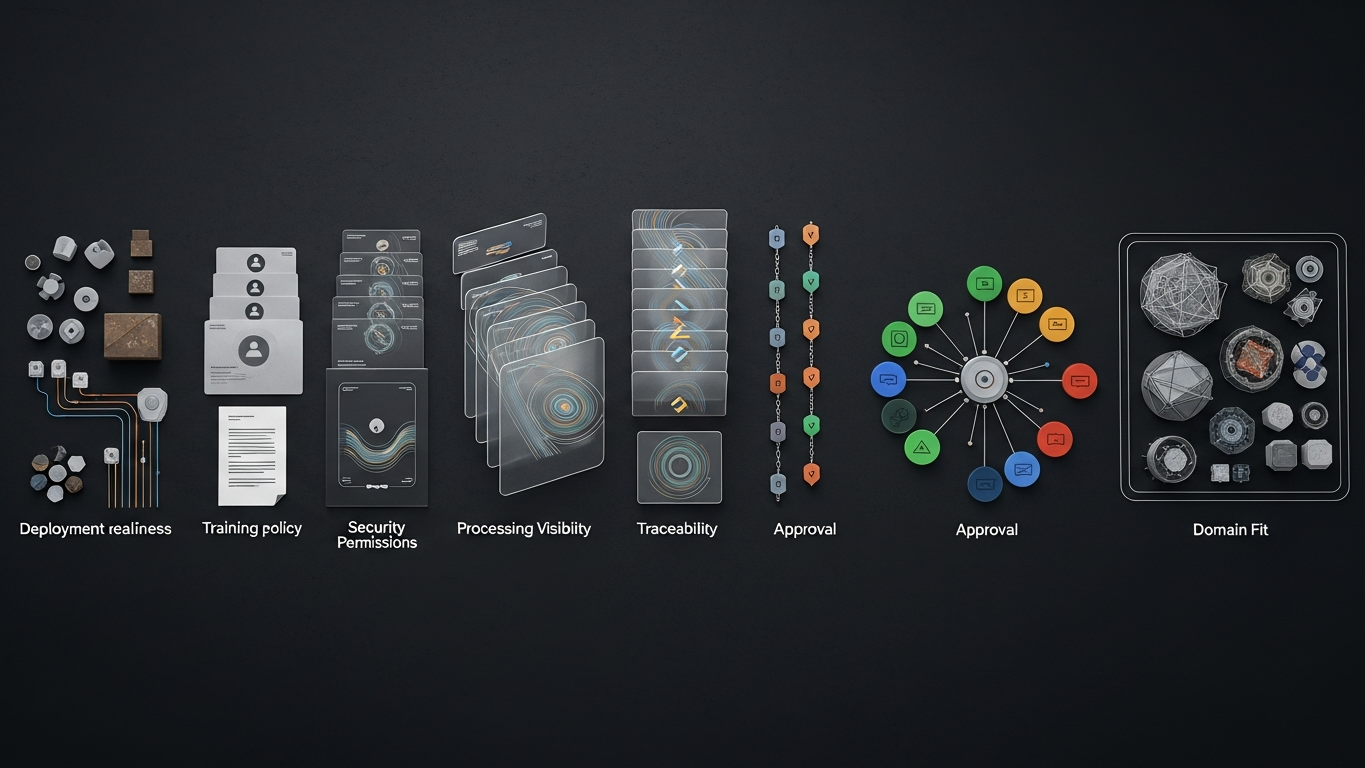
Before adopting AI in a manufacturing environment, buyers should verify deployment boundary (can the model run in a setup that matches your control requirements?), training policy (are client data and prompts excluded from model training?), access control (is access limited, logged, and reviewable?), processing visibility (can you understand how data moves and is handled?), traceability (can outputs, approvals, and actions be reconstructed?), human approval (do high-consequence workflows keep the right review layers?), and domain fit (does the system reflect industrial reasoning rather than generic AI convenience?).
Why each item matters
This checklist works because it covers the full AI operating model: control, data protection, governance, accountability, and usefulness. If one layer is weak, the overall deployment becomes harder to trust—even if the model produces attractive text. Industrial adoption is not a single-attribute purchase. It is a bundle, and the bundle has to hold under review.
How buyers should use the checklist
The checklist should not be used only at procurement. It should also be used during vendor comparison, pilot design, security review, and governance review. That discipline makes adoption more coherent from the start: fewer “temporary” exceptions that become permanent, fewer shadow paths that appear because nobody wanted to slow the demo.
What weak answers usually look like
Manufacturers should slow down when answers are vague, overly marketing-led, too dependent on future promises, or disconnected from workflow consequence. Secure industrial AI should survive concrete questioning—the kind of questioning your own teams will ask the first time something goes wrong on a Friday.
Pass/fail mindset: if an item cannot be verified with artifacts (diagrams, contract language, log samples), it is not yet closed.
DBR77 Vector is positioned around the conditions enterprise buyers increasingly need: private deployment options, no training on client data, industrial reasoning, stronger governance expectations, and human approval over critical decisions. That makes it easier to evaluate through a real checklist instead of vague assurance.
The fastest way to evaluate secure AI in manufacturing is to use a checklist that tests deployment, training policy, access, traceability, approval, and domain fit. Serious industrial AI should be able to answer each of these clearly.
Plant checkpoint
Treat “The Enterprise Checklist for Secure AI in Manufacturing” as a decision tool, not background reading. Before the next steering meeting, ask for one artifact that proves your posture—an architecture diagram, a training-policy excerpt, a log sample, a signed workflow classification, or a promotion record. If the room can only tell stories, you are still in pilot clothing. Manufacturing AI matures when evidence becomes routine: the same discipline you already expect before a line release, a supplier change, or a major IT cutover. That is the shift from excitement to infrastructure—and it is what keeps programs coherent across audits, turnover, and multi-site expansion.
If leadership wants one crisp decision habit, make it this: name what must be true before usage expands, then review whether it is true on a fixed cadence. That is how governance stops being a narrative comfort and becomes an operating metric your plants can execute.
DBR77 Vector gives enterprise buyers a stronger secure-AI checklist fit through private deployment, no training on client data, industrial reasoning, and governed approvals. Review security or Review deployment options.
